Zero Trust Network Access
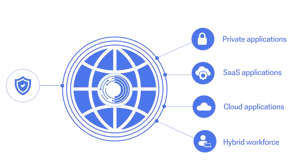
Cisco Duo's Zero Trust Network Access (ZTNA) solution secures all access across your applications and environment, from any user, device and location.
Zero Trust Network Access
Cisco Duo's Zero Trust Network Access (ZTNA) solution secures all access across your applications and environment, from any user, device and location.

Benefits of Orixcom ZTNA
Apply contextual policies based on user role, location, device type, and risk level. Grant least-privilege access to protect sensitive resources.

with ZTNA
Zero Trust Network Access (ZTNA) delivers secure, identity-based access to applications, no matter where users are located. By verifying user identity and device health before granting access, ZTNA ensures only authorised users connect to the resources they need.
ZTNA also integrates seamlessly with Duo MFA, enabling fast, secure authentication via Duo Push. Combined with adaptive access policies and full visibility into user devices, it creates a resilient framework for secure remote work.
With Cisco ZTNA, implicit trust is eliminated. Access is granted based on context, such as user role, location, and device posture reducing the risk of lateral movement and protecting sensitive data.
This approach strengthens your remote access strategy while minimising attack surfaces, ensuring that only trusted users and devices interact with your critical applications.
Discover more about
Orixcom ZTNA
Trusted by

Better together
Safeguard your organisation from cyberattacks with Cisco Umbrella
will build the right combination for your business.
ZTNA is a security approach that assumes no user or device is trusted by default and grants access only to specific applications based on identity, device health, and context. It reduces the attack surface by avoiding broad network access and instead providing controlled, application‑level access.
Implement a zero trust strategy today
Enable secure, seamless access for all users, across any device, location, or application.

.webp?width=300&name=achieving-zero-trust-with-sd-wanthe-foundation-of-a-sase-enabled-architecture%20(1).webp)
